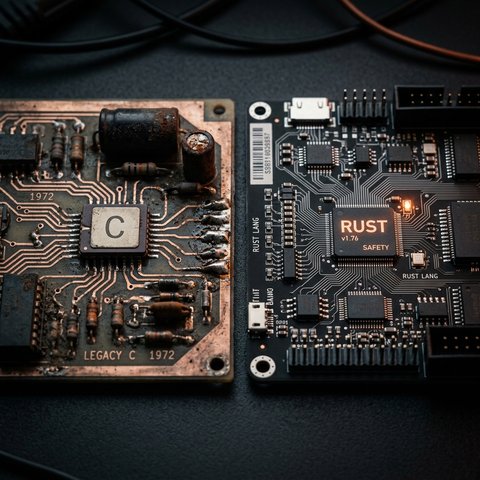
The Succession War: Rust vs. C in 2026
In 1972, Dennis Ritchie created C at Bell Labs. It was a language of radical simplicity: a thin abstraction over the PDP-11's instruction set that gave the programmer absolute dominion over the machine. Fifty-four years later, that dominion remains the backbone of virtually every operating system, embedded controller, and database engine on the planet. But in 2026, C faces its most credible challenger yet. Rust, born at Mozilla Research in 2010, has crossed the threshold from promising experiment to institutional mandate. The question is no longer whether Rust is a viable alternative to C. The question is whether C, in its current form, is a viable choice for new systems-level development.
This is not a puff piece for either language. As an engineer who has spent years in both ecosystems, I believe the answer is far more nuanced than the tribal warfare on developer forums would suggest. Let's examine the evidence.
I. The Memory Safety Crisis: C's Original Sin
The single most consequential difference between Rust and C is memory safety, and the data is unambiguous. Research from Microsoft and Google, consistently replicated across the industry, shows that approximately 70% of serious security vulnerabilities—the kind that lead to arbitrary code execution, data breaches, and infrastructure compromise—are caused by memory safety errors. Buffer overflows, use-after-free, double-free, and dangling pointers: these are not exotic edge cases. They are the bread and butter of vulnerability research, and they are endemic to C.
In C, memory management is entirely manual. The programmer allocates with malloc, deallocates with free, and is responsible for every pointer's lifecycle. This model offers extraordinary flexibility, but it relies entirely on human discipline. Static analyzers and sanitizers like AddressSanitizer and Valgrind can catch many errors, but they cannot guarantee their absence. The uncomfortable truth is that no amount of tooling can make C provably memory-safe without fundamentally changing the language itself.
Rust addresses this with its ownership and borrowing system, enforced entirely at compile time. Every value in Rust has a single owner. References are either shared and immutable, or unique and mutable—never both simultaneously. When an owner goes out of scope, memory is freed deterministically, with no garbage collector overhead. The result is that entire classes of vulnerabilities are eliminated before the program ever runs. This is not a runtime check; it is a mathematical guarantee enforced by the compiler. The cost is a steeper learning curve and a compiler that sometimes feels like an adversary, but the payoff is a level of safety that C simply cannot provide.
II. Performance: The Myth of the 'Rust Tax'
A persistent myth in systems programming circles is that safety comes at a performance cost. In the case of Rust versus C, this is largely false. Both languages offer zero-cost abstractions—high-level features that compile down to machine code with no runtime overhead. In 2026, comprehensive benchmarks consistently show that Rust and C perform within single-digit percentages of each other in most real-world workloads, with the winner varying by task.
C can still edge out Rust in highly specific microbenchmarks—certain tight numerical loops or hand-optimized SIMD operations where the programmer exploits decades of compiler maturity in GCC and Clang. But these are diminishing advantages. LLVM, which serves as the backend for both Clang (C) and rustc (Rust), is converging the performance profiles of both languages. More importantly, in real-world concurrent applications—the kind that dominate modern infrastructure—Rust often holds an advantage. Its compile-time guarantee of data-race freedom allows developers to write fearlessly concurrent code without the overhead of complex mutex hierarchies or the risk of subtle race conditions that plague multithreaded C programs.
III. Concurrency: Where Rust Pulls Ahead
This deserves its own section because it is, in my view, Rust's most underappreciated advantage. Concurrency in C is a minefield. Pthreads are powerful but unforgiving. A missed lock, a shared mutable state accessed without synchronization—these are bugs that may not manifest for months of production runtime, only to surface as a catastrophic, non-reproducible crash under peak load. The tooling to detect them (ThreadSanitizer, Helgrind) is good but not exhaustive, and it adds significant runtime overhead during testing.
Rust's type system makes data races a compile-time error. If you try to share mutable data across threads without proper synchronization (via Arc<Mutex<T>> or channels), the code simply will not compile. This is a paradigm shift. It transforms concurrency from a source of latent, fear-inducing bugs into a composable, verifiable property of the program. For distributed systems and high-throughput infrastructure—precisely the kind of code that defines modern cloud computing—this is not just convenient; it is transformative.
IV. The Political and Institutional Pressure
Beyond technical merits, there is a powerful political dimension driving the shift. In 2026, this is no longer a grassroots movement. CISA, the FBI, and the Office of the National Cyber Director have explicitly stated that not having a published memory safety roadmap by January 1, 2026, is 'dangerous' and a significant elevation of risk to national security. The message from the U.S. government is clear: using memory-unsafe languages for new product lines in critical infrastructure, where memory-safe alternatives exist, is now formally classified as a 'Product Security Bad Practice.'
This pressure is translating into action at the highest levels. Rust is no longer experimental in the Linux kernel; it is a permanent, supported subsystem alongside C and Assembly for developing drivers and modules. Microsoft has integrated Rust into specific components of the Windows kernel, including parts of DirectWrite and GDI. Google mandates Rust for new Android platform code. These are not experiments; they are strategic, institutional commitments to a language that offers safety guarantees that C fundamentally cannot.
V. Where C Remains Indispensable
It would be intellectually dishonest to conclude that C is obsolete. It is not, and it will not be for a very long time. In deeply embedded systems—the world of 8-bit microcontrollers, hard real-time loops, and safety-critical domains certified under ISO 26262 or DO-178C—C remains the undisputed king. The reason is not technical superiority, but institutional inertia and toolchain qualification. Certifying a compiler and its runtime for use in avionics or automotive safety systems is a multi-year, multi-million-dollar process. Rust's toolchain has not yet achieved this level of formal qualification in most safety-critical verticals.
Furthermore, C's ABI stability is unmatched. It is the lingua franca of inter-language communication. Nearly every language on Earth—Python, Go, Java, Rust itself—provides a Foreign Function Interface (FFI) that speaks C. Replacing C's ABI would require replacing the very foundation of software interoperability, a task that is orders of magnitude harder than replacing C the language.
VI. The Verdict: Coexistence, Not Conquest
The 2026 reality is one of complementary coexistence. New, high-criticality, security-sensitive code is increasingly and rightly being written in Rust. Legacy C codebases—representing trillions of lines of battle-tested infrastructure—will be maintained, hardened, and gradually refactored, not wholesale rewritten. The industry has adopted a mixed-language approach: Rust for the new frontier, C for the established foundation, with a clear trajectory of Rust absorbing more of the critical surface area over time.
As an engineer, my advice is pragmatic. If you are starting a new systems-level project in 2026 and you choose C over Rust without a compelling, domain-specific reason—such as a certified toolchain requirement or a target platform with no Rust support—you are making a choice that is increasingly difficult to justify to your security team, your compliance officers, and your government regulators. But if you are maintaining a critical C codebase, your path is hardening, not panic. Invest in static analysis, adopt smart pointers where the standard permits, and build a roadmap for introducing Rust at the boundaries.
The Succession War is not about one language 'winning.' It is about the engineering discipline maturing enough to demand that its most fundamental tools—the ones that build the operating systems, the kernels, the network stacks—are as safe as they are fast. In that war, the real winner is the engineer who understands both the legacy and the future, and knows precisely where to draw the line.